- I tested Hisense's flagship QLED TV and didn't miss my OLED set (especially when it's $700 off)
- Next-gen AI chips will draw 15,000W each, redefining power, cooling, and data center design
- Amazon extends July Prime Day to four day event, confirms 2025 dates
- Edge reality check: What we've learned about scaling secure, smart infrastructure
- Salesforce study warns against rushing LLMs into CRM workflows without guardrails
Experts Warn of Hacking Group Targeting Aviation and Defense Sectors

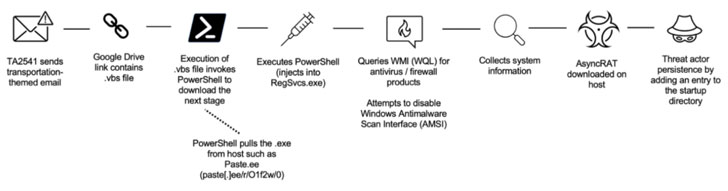
Entities in the aviation, aerospace, transportation, manufacturing, and defense industries have been targeted by a persistent threat group since at least 2017 as part of a string of spear-phishing campaigns mounted to deliver a variety of remote access trojans (RATs) on compromised systems.
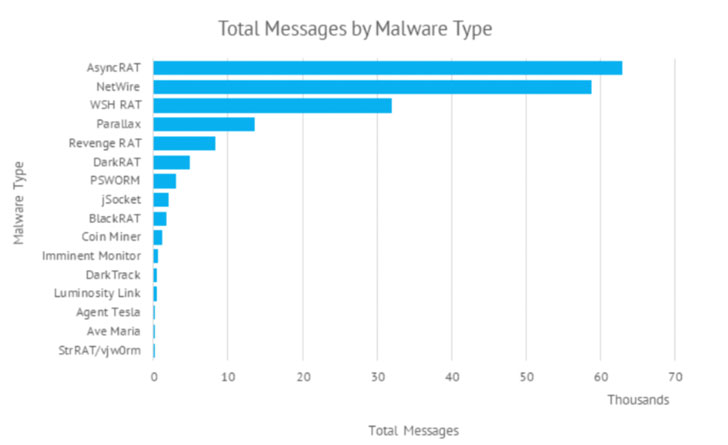
The use of commodity malware such as AsyncRAT and NetWire, among others, has led enterprise security firm Proofpoint to a “cybercriminal threat actor” codenamed TA2541 that employs “broad targeting with high volume messages.” The ultimate objective of the intrusions is unknown as yet.
Social engineering lures used by the group does not rely on topical themes but rather leverages decoy messages related to aviation, logistics, transportation, and travel. That said, TA2541 did briefly pivot to COVID-19-themed lures in the spring of 2020, distributing emails concerning cargo shipments of personal protective equipment (PPE) or testing kits.
“While TA2541 is consistent in some behaviors, such as using emails masquerading as aviation companies to distribute remote access trojans, other tactics such as delivery method, attachments, URLs, infrastructure, and malware type have changed,” Sherrod DeGrippo, vice president of threat research and detection at Proofpoint, told The Hacker News.
The campaigns have historically utilized macro-laden Microsoft Word attachments to drop the RAT payloads, although recent variants include links to cloud services hosting the malware. The phishing attacks are said to strike hundreds of organizations globally, with recurring targets observed in North America, Europe, and the Middle East.
The repeated use of the same themes aside, select infection chains have also involved the use of Discord app URLs that point to compressed files containing AgentTesla or Imminent Monitor malware, indicative of the malicious use of content delivery networks to distribute information gathering implants for remotely controlling compromised machines.
“Mitigating threats hosted on legitimate services continues to be a difficult vector to defend against as it likely involves implementation of a robust detection stack or policy-based blocking of services which might be business-relevant,” DeGrippo said.
Other techniques of interest employed by TA2541 include the use of Virtual Private Servers (VPS) for their email sending infrastructure and dynamic DNS for command-and-control (C2) activities.
With Microsoft announcing plans to turn off macros by default for internet-downloaded files starting April 2022, the move is expected to cause threat actors to step up and shift to other methods should macros become an inefficient method of delivery.
“While macro-laden Office documents are among the most frequently used techniques leading to download and execution of malicious payloads, abuse of legitimate hosting services is also already widespread,” DeGrippo explained.
“Further, we regularly observe actors ‘containerize’ payloads, using archive and image files (e.g., .ZIP, .ISO, etc.) which also can impact ability to detect and analyze in some environments. As always, threat actors will pivot to use what is effective.”